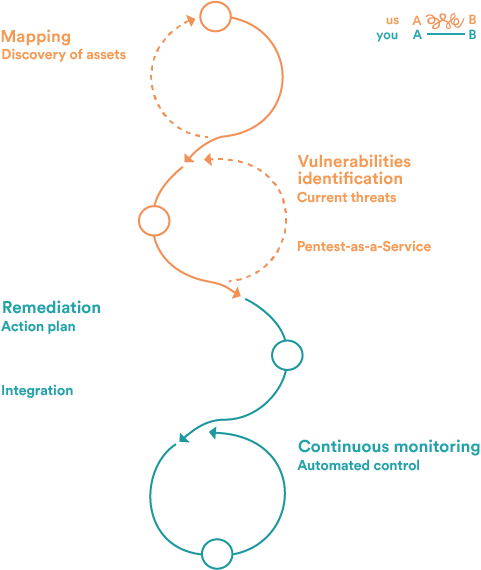
The attack surface encompasses all entry points that can be exploited by an attacker: exposed services, vulnerabilities, misconfigurations or human errors. The wider it is, the higher the risk of intrusion.
Within a Continuous Threat Exposure Management (CTEM) approach, its management relies on five pillars:
Continuously identify exposures
Analyze and prioritize based on real impact and exploitability
Reduce the surface by removing unnecessary access points
Rapidly remediate critical vulnerabilities
Minimize response time between detection and remediation
CTEM enables organizations to continuously adapt their security strategy to evolving threats and sustainably strengthen their security posture.